Observations on cyber threat activity and vulnerabilities in the Gulf Region
May 31, 2023
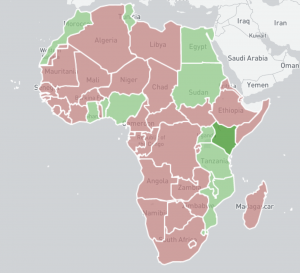
We are happy to continue our efforts in collaboration with the UK FCDO, building on our previous global outreach to Africa, Indo-Pacific, Central and Eastern Europe (CEEC), and Association of Southeast Asia Nations (ASEAN) regions to produce a cyber security spotlight on the Gulf Region. For a review of previous UK FCDO supported activities please read a) UK Foreign, Commonwealth & Development Office funds Shadowserver surge in Africa and Indo-Pacific regions, b) Continuing Our Africa and Indo-Pacific Regional Outreach, c) More Free Cyber Threat Intelligence For National CSIRTs and d) Shadowserver’s New Public Dashboard.