Rhadamanthys Historical Bot Infections Special Report
November 13, 2025
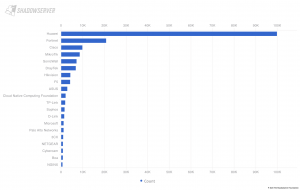
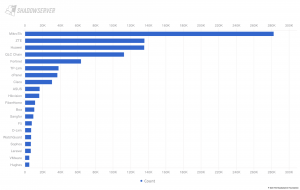
On Thursday 13th November 2025, international law enforcement partners announced a disruption action against the Rhadamanthys information stealer malware. As part of the ongoing Operation Endgame initiative, law enforcement acquired copies of the threat actor’s databases containing historical Rhadamanthys infections, which covered the period March 2025 to November 2025. These databases contain records of over 86 million stolen data items from over 525,000 Rhadamanthys infections across 226 countries. Shadowserver is sharing elements of this dataset as a one-off Special Report, to allow historical Rhadamanthys infections to be investigated and any secondary malware identified and remediated by system defenders.