Tycoon 2FA Phishing-as-a-Service Disruption
March 5, 2026
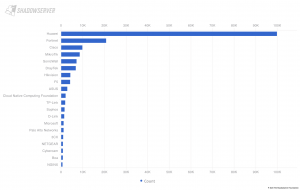
On March 4th 2026, a coalition of Law Enforcement and private sector partners announced a major international public-private disruption operation targeting Tycoon 2FA. This leading phishing-as-a-service platform was used by thousands of cybercriminals to bypass multi-factor authentication and enable large-scale account compromise globally. Details of the operation were shared by partners and a new Shadowserver National CSIRT-only Special Report was run, sharing data about observed Tycoon 2FA infrastructure domains. Analysis of the reported Tycoon 2FA domains is provided.