Shadowserver Report Provides Cybersecurity Insights and Recommendations for ECOWAS Member States in West Africa
June 8, 2026
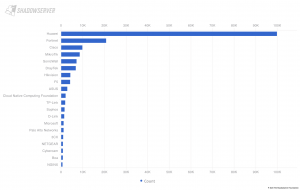
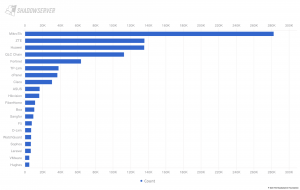
Shadowserver issued a report to inform government leaders, policymakers, and other key stakeholders in ECOWAS Member States in West Africa on the following: a) The ECOWAS region’s cyber threat landscape and attack surface using Shadowserver’s free, actionable cyber threat intelligence, technical analysis, and expert insights b) The region’s institutional and operational cybersecurity deficiencies (“gaps”) that make it increasingly vulnerable to cyber threats c) Recommended actions that can be undertaken at the national and regional levels to address the identified gaps, improve digital security, and enhance cyber resilience in the region d) The potential economic and societal impact should the identified institutional and operational cybersecurity gaps remain unaddressed.