Shadowserver Special Reports are a NEW type of free, one off report. They do not cover a specific time period. We will send out Special Reports whenever we are able to share one-time, high value datasets that we feel should be reported responsibly for maximum public benefit. Although the events included in these Special Reports will fall outside of our usual 24 hour daily reporting window, we believe that there would still be significant benefit to our constituents in receiving and hopefully acting on the retrospective data.
This new Special Report – Vulnerable Exchange Servers Special Report #2 – is our third Special Report, following hot on the heels of yesterday’s two initial Special Reports:
1. HAFNIUM Exchange Special Report (covering activity from the pre-Microsoft Exchange Server patch release period 2021-02-26 to 2021-03-03)
2. Vulnerable Exchange Servers Special Report #1 (covering activity from the post-Microsoft Exchange Server patch release period on 2021-03-09)
This time we have partnered with KryptosLogic, who have also kindly offered to share data from an Internet scan performed today (2021-03-12) to detect web shells that were likely dropped by exploitation of the recently disclosed CVE-2021-26855, CVE-2021-26857, CVE-2021-26858 and CVE-2021-27065 vulnerabilities in Microsoft Exchange Server. Mass attacks have been widely reported to be now being performed by multiple threat actor groups, so this data is not being attributed to the HAFNIUM threat actor group. It likely to be other “early adopter” APT groups and likely also by mainstream cybercriminals too). Thank you KryptosLogic for being willing to quickly share their data with victims globally for public benefit.
The total dataset distributed to 120 National CSIRTs in 148 countries and over 5900 network owners covers 6720 unique web shell URL paths corresponding to 5818 unique IP addresses that were assessed on 2021-03-12 as being compromised Microsoft Exchange Servers with active webshells on common URL paths. Note that some IP addresses have multiple web shell URI paths (presumably from multiple compromises). Anyone with the simple, easy to guess URL for any of these web shells could potentially compromise more of your infrastructure. We strongly encourage network owners and National CERT/CSIRTs urgently remediate and patch/rebuild all impacted victim systems immediately.
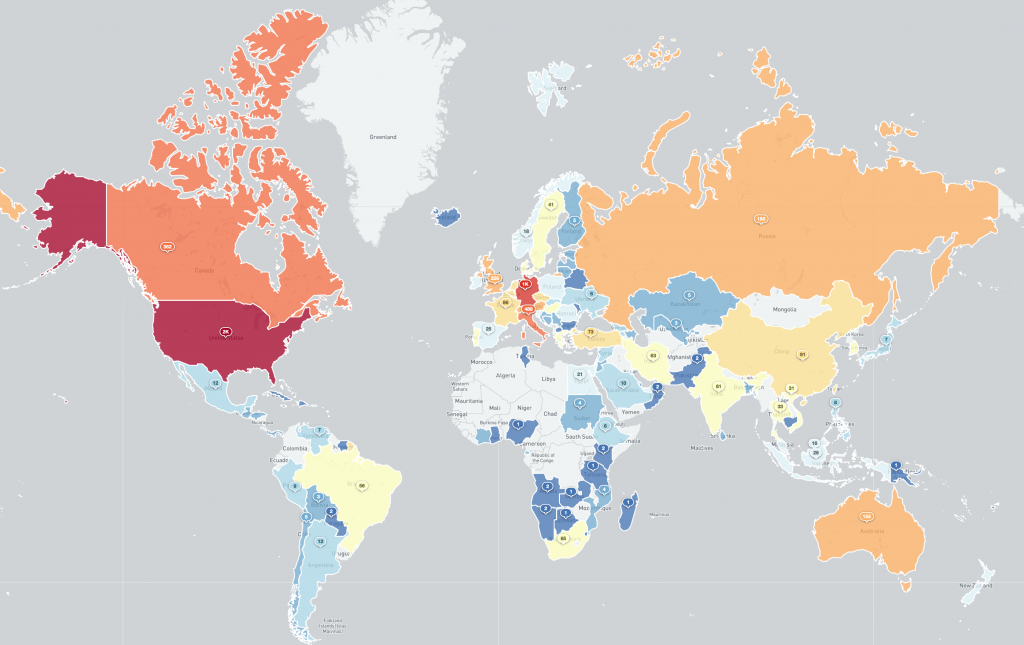
Countries with compromised Microsoft Exchange servers with public exposed web shells 2021-03-12 (log scale):
Countries with compromised Microsoft Exchange servers with public exposed web shells 2021-03-12 (interactive):
Countries with compromised Microsoft Exchange servers with public exposed web shells 2021-03-12 (treemap):
You can find more detail on the format of the new Special Report here.
Remediation advice for Microsoft Exchange Server operators has been provided by CISA. Microsoft have released tools for checking Exchange servers for evidence of exploitation. You can also use the online CheckMyOWA resource to check if your Exchange Server has appeared in their data.
If you have missed this Special Report because you were not yet a subscriber to our free daily network reports, do not worry: simply subscribe for your network or country now and specifically request all recent Shadowserver Special Reports. We will resend the Special Report specifically for your network or country (for National CERT/CSIRTs).
If you have a data set which you feel could also be of benefit to National CERT/CSIRTs and network owners world-wide to help protect victims of cybercrime, please get in touch and discuss the options for using Shadowserver’s proven reporting systems for distribution and remediation.
We hope that the new Shadowserver Special Reports will be a useful additional free tool in helping network defenders identify victims and better protect their networks and the entire Internet. Please contact us if you have any questions.