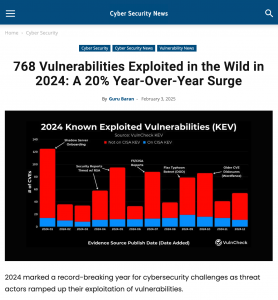
Cyber Security News, February 3, 2025
According to the latest findings from VulnCheck, 768 Common Vulnerabilities and Exposures (CVEs) were publicly reported as exploited in the wild for the first time this year (2024). Spikes in exploitation reporting frequently coincided with major industry events, including the RSA Conference, or were influenced by disclosures from newly onboarded sources like ShadowServer. ShadowServer’s integration into reporting processes in January also led to increased public awareness of exploitation.
The 2024 report highlighted that the initial evidence of exploitation came from a diverse set of 112 unique sources, underscoring the importance of collaboration within the security community. These sources include: Third-party security vendors, Government Agencies; Non-profits: Groups like ShadowServer significantly contributed to disclosure efforts; Product Vendors; and Independent Platforms.