Ivanti VPN Appliances Patch Critical Heap Overflow Bug
The cybersecurity community is on high alert after uncovering a serious flaw in Ivanti VPN devices, tracked as CVE-2024-21894. This critical vulnerability holds grave consequences for entities relying on Ivanti for secure remote access. The threat posed by this exploit is considerable, as it could allow unauthorized remote control over affected systems, endangering both operational integrity and the confidentiality of sensitive information. Businesses employing Ivanti’s VPN must act swiftly to implement necessary safeguards.
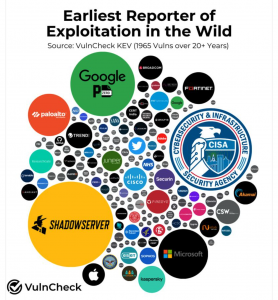
The Shadowserver Foundation’s extensive network scanning has cast a spotlight on a significant security concern—a widespread vulnerability in the Ivanti VPN software, evidenced by the startling discovery of over 16,000 instances at risk to the critical vulnerability designated as CVE-2024-21894. The Shadowserver Foundation has played a crucial role in unmasking the extent of exposure, which suggests that the issue is not isolated but rather prevalent, raising the alarm on an international scale. Encouragingly, a follow-up check conducted by Shadowserver as of April 7 indicated a reduction in the number of vulnerable instances—to about 10,000.
Shadowserver stands as a key player in the cybersecurity field, relentlessly scanning the internet to pinpoint vulnerabilities. Their role is critical; by detecting and alerting firms to security gaps, they enable proactive defense strategies. Their efforts reflect a significant, broader principle in cybersecurity: collaboration is essential. As a vigilant entity that assists with early threat detection and raises community awareness about evolving digital dangers, Shadowserver functions as a vital component in the fight to protect online environments against nefarious elements. By doing so, they are not just guards but catalysts of collective cyber resilience, underscoring the shared responsibility in defending cyber spaces. Through Shadowserver’s dedication, the digital world becomes a bit more fortified against the constant threat of cyber incursions.