On March 4th 2026, a major international public-private disruption operation was announced that aimed to take down Tycoon 2FA.
What is Tycoon 2FA?
Tycoon 2FA is one of the leading phishing-as-a-service platforms used to bypass multi-factor authentication (MFA) and enable large-scale account compromise globally, and has been a major driver of initial access and large-scale online impersonation attacks. It provides cybercriminals with a subscription-based toolkit designed to intercept live authentication sessions and gain unauthorised access to online accounts, including those protected by additional security layers.
Unlike traditional phishing kits, Tycoon 2FA was designed to defeat security protections intended to improve user account security, including MFA. It features convincing phishing templates, realistic landing pages, and real‑time capture of credentials and authentication codes – all sold to cybercriminals in an easy‑to‑use package, enabling them to target large numbers of victims globally.
Tycoon 2FA has been active since at least August 2023, and was among the largest phishing operations worldwide. It enabled thousands of cybercriminals to covertly access email and cloud-based service accounts. The platform generated tens of millions of phishing emails each month and facilitated unauthorised access to nearly 100,000 organisations globally, including schools, hospitals, and public institutions. Healthcare and education organizations were hit hardest, which led to 100+ members of Health‑ISAC, a global threat-sharing group for the health sector, being a co-plaintiff with Microsoft in a US civil legal action against the threat actors:
According to partner analysis, by mid-2025, Tycoon 2FA accounted for roughly 62% of all phishing attempts blocked by Microsoft, including more than 30 million emails in a single month. The criminal service has been linked to an estimated 96,000 distinct phishing victims worldwide since 2023, including more than 55,000 Microsoft customers.
Tycoon 2FA Disruption
The disruption operation was carried out by a coalition of international Law Enforcement partners and private sector stakeholders, who worked hand in hand to systematically tackle this major threat. The operation was coordinated by Europol’s European Cybercrime Centre (EC3).
Intelligence was shared by Trend Micro, Microsoft and The Shadowserver Foundation through Europol’s Cyber Intelligence Extension Programme (CIEP), which aims to strengthen public-private cooperation in tackling cybercrime by enabling trusted private-sector partners to contribute actionable intelligence and support operational outcomes. The CIEP programme – a first of its kind – brings together experts from the private sector to work temporarily side by side in The Hague on specific projects with EC3 analysts and investigators.
Disrupting Tycoon 2FA required legal, technical and logistical activities that spanned multiple jurisdictions. Operation partners worked together closely, and included:
Law enforcement authorities
- Latvia: State Police
- Lithuania: Criminal Police Bureau
- Portugal: Judicial Police
- Poland: Central Cybercrime Bureau
- Spain: National Police and Guardia Civil
- United Kingdom: National Crime Agency
Private partners engaged through Europol (with links to each of their own blog posts about the Tycoon 2FA operation provided):
- Cloudflare
- Coinbase
- Intel471
- Microsoft
- Proofpoint
- The Shadowserver Foundation
- SpyCloud
- Trend Micro
As is typical of many major cybercrime disruption efforts, no single organization could have assembled the full intelligence/investigative picture and tackled this major threat alone. The combined activities of the partners disrupted one of the most significant enablers of identity-based attacks globally, whose administrators and users targeted identity instead of infrastructure.
New Shadowserver Tycoon 2FA Domains Special Report
On March 4th 2026, Shadowserver ran a new, one-off, National CSIRT-only Tycoon 2FA Domains Special Report. It contained information about domain names that were assessed by partners to have been used in the operation of the Tycoon 2FA phishing-as-a-service platform. Domain registration start and end dates were between 2023-03-19 and 2027-04-03 (since active domains could expire up to twelve months after registration).
Our 2026-03-04 Tycoon 2FA Domains Special Report contained 25,206 events and was delivered to 237 National CSIRTs globally.
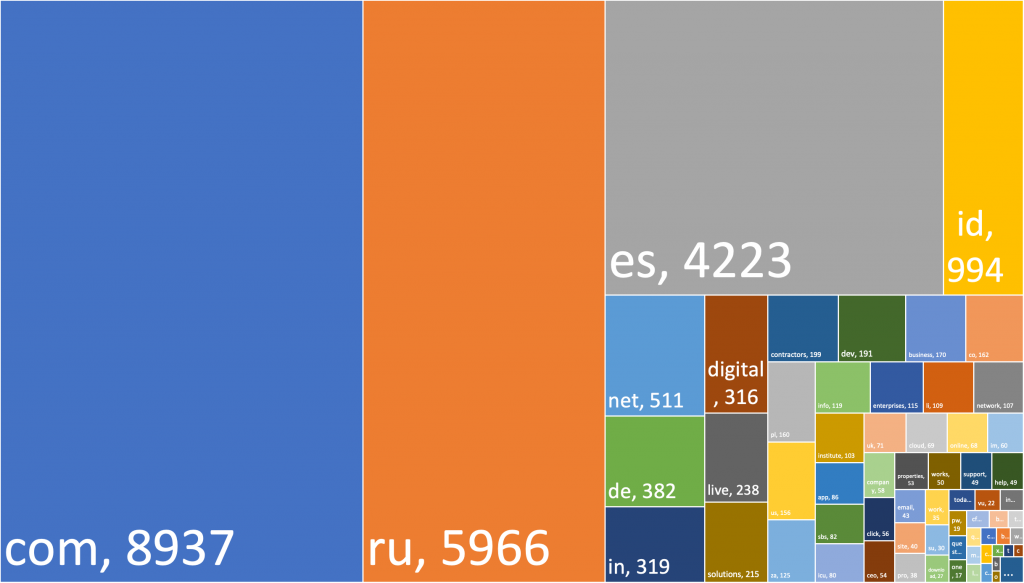
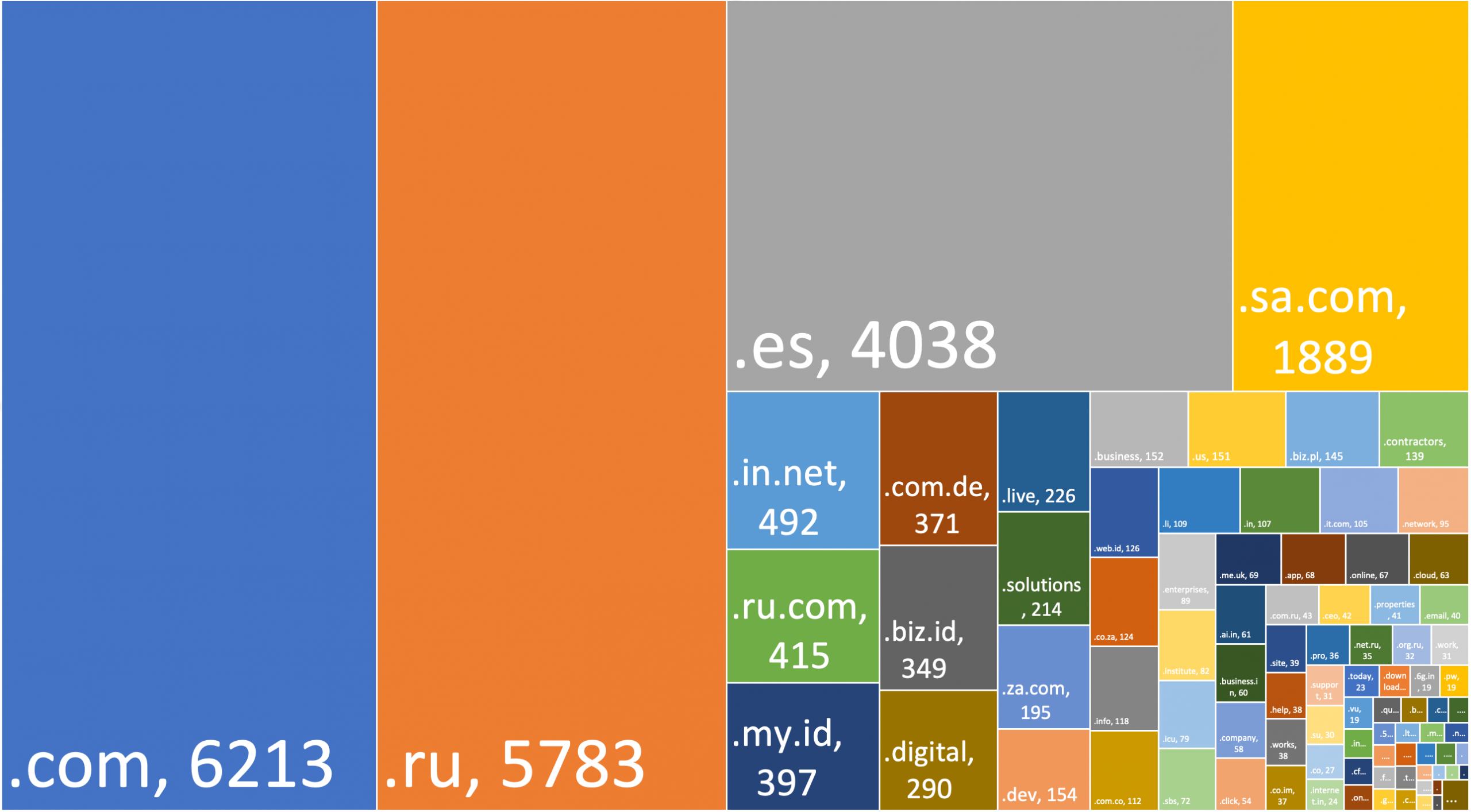
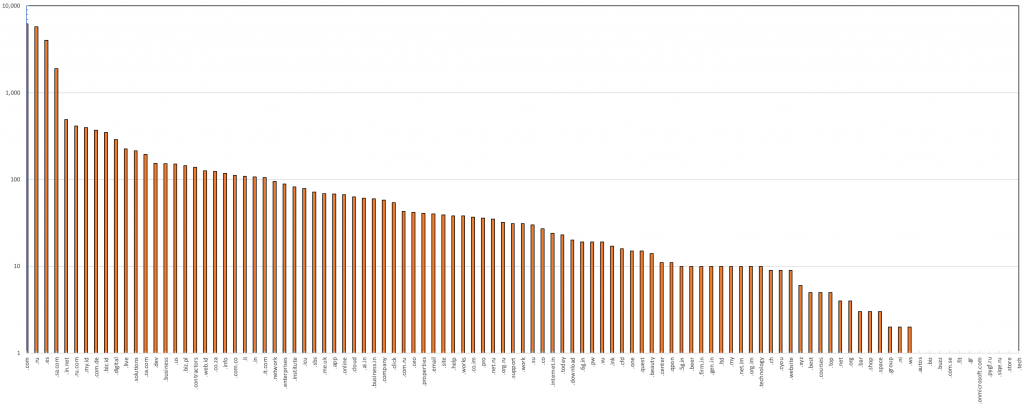
The domains corresponded to the following Top Level Domains (TLDs):
Figure 1 – Treemap of Tycoon 2FA domain TLDs (apex level)
Figure 2 – Treemap of Tycoon 2FA domain TLDs (second level)
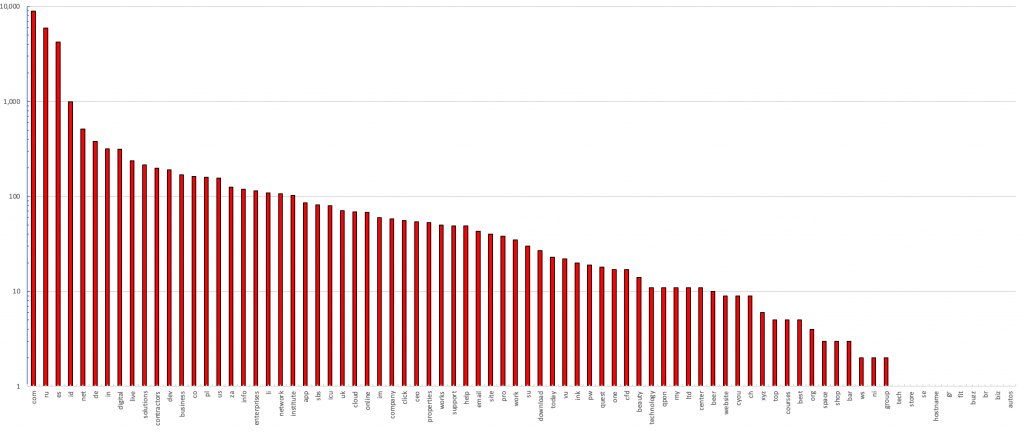 Figure 3 – Graph of Tycoon 2FA domain TLDs (apex level, logarithmic)
Figure 3 – Graph of Tycoon 2FA domain TLDs (apex level, logarithmic)
Figure 4 – Graph of Tycoon 2FA domain TLDs (second level, logarithmic)
At the time the Tycoon 2FA Domains Special Report was run, 8,702 of the domains resolved to 6,754 unique IP addresses. These were hosted across 56 different Autonomous System Numbers (ASNs) and geo-located to 22 different countries.
Note: Domains that were assessed to be active Tycoon 2FA panel/command control (C2) infrastructure between 2023-03-19 and 2026-03-03 have since been suspended, parked, sinkholed, become non-malicious, or expired and were re-registered. So while the data provided can be used to hunt for historical indications of network activity between the stated first_seen_time and last_seen_time, which may indicate past or current malicious activity in constituent networks, the current domain to IP address resolution at the time the Special Report was run (2026-03-04) and this analysis of ASN, country and IP-geolocation data is only provided for interest to represent the state of the domains at this particular point in time.
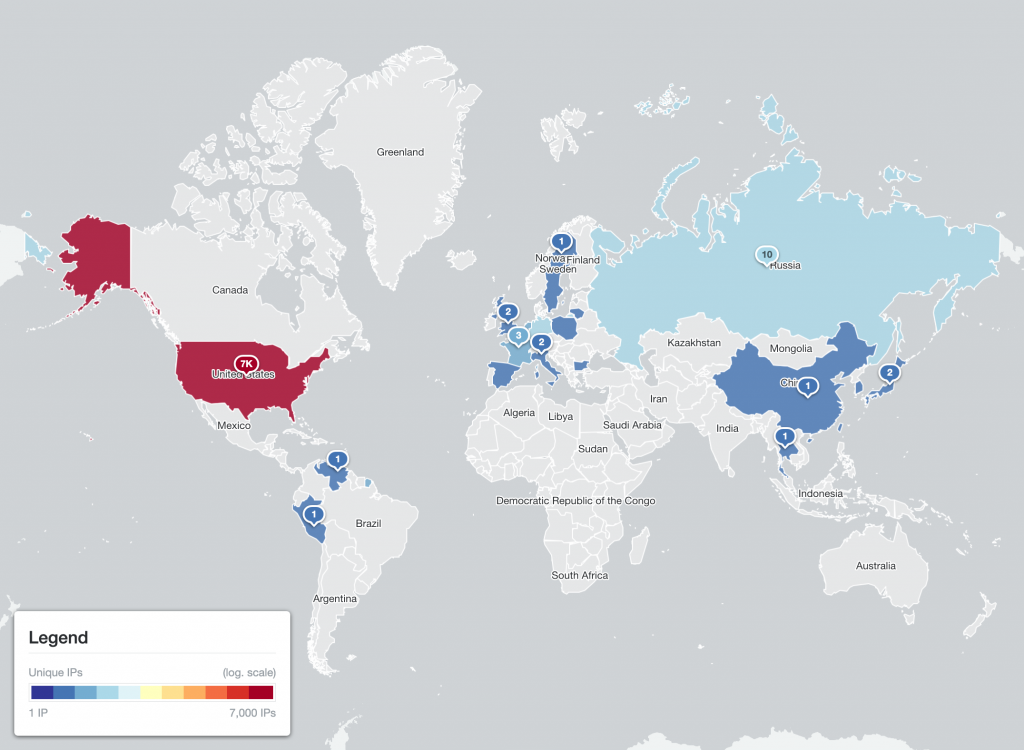 Figure 5 – Worldmap of Tycoon 2FA domain IP geolocations (only the subset that resolved to an IP address on 2026-03-04)
Figure 5 – Worldmap of Tycoon 2FA domain IP geolocations (only the subset that resolved to an IP address on 2026-03-04)
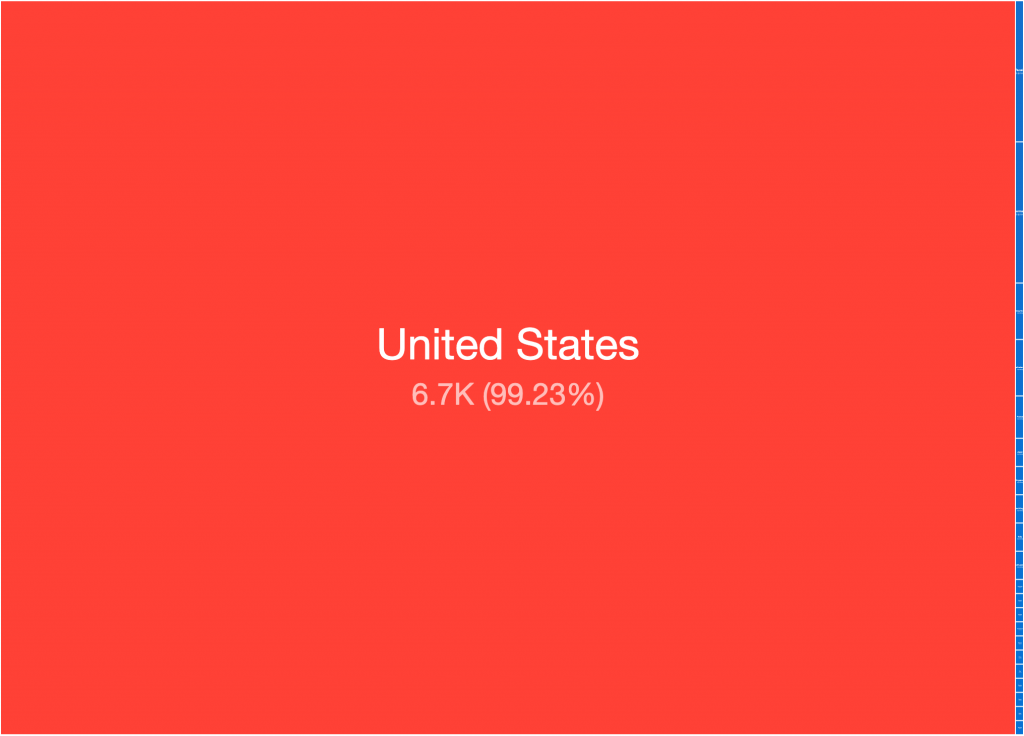 Figure 6 – Treemap of Tycoon 2FA domain IP geolocations (only the subset that resolved to an IP address on 2026-03-04)
Figure 6 – Treemap of Tycoon 2FA domain IP geolocations (only the subset that resolved to an IP address on 2026-03-04)
You can find more details, including the technical specifications, data format, example data, and how to request the data again if you need help accessing it, on our Tycoon 2FA Domains Special Report page:
As a contributor to the joint international disruption operation, Shadowserver also provided expert advice to our trusted partners on domain seizures, worked with international LE partners on acquiring addition panel/C2 domains, hosted some of the take down “splash pages” used to notify Tycoon 2FA users and administrators that their domains had been seized, and registered a number of expired C2/campaign domains to prevent them being re-registered.
This operation represents an interesting twist on traditional approaches to cybercrime investigations. Typically, Law Enforcement investigations are instigated following victim allegations of reported crimes. Investigators, having undertaken a reactive investigation, often reach out to trusted private sector partners for assistance. However, in this case, the private sector pro-actively approached Europol via their CIEP program about an international crime problem, and Law Enforcement embraced joint working. Collaboration in this manner requires both the public and private sector to work in subtly different ways to their normal processes. The net result is a model that offers greater impact for the general public than either might achieve alone. We look forward to continuing to collaborate successfully with our trusted international partners, and supporting more successful disruption operations in the future.
If you have any questions, please contact us, although there may be limitations on what information can be shared at this time due to the ongoing LE investigations.
Thank you to the UK Foreign, Commonwealth and Development Office (FCDO) and UK Integrated Security Fund (ISF) for supporting The Shadowserver Foundation’s public benefit mission and enabling us to continue to provide free support to our international Law Enforcement partners on another successful cybercrime disruption operation.