CISA's KEV Catalog Updated with 3 New Flaws Threatening IT Management Systems
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.The list of vulnerabilities is below –
- CVE-2022-35914 (CVSS score: 9.8) – Teclib GLPI Remote Code Execution Vulnerability
- CVE-2022-33891 (CVSS score: 8.8) – Apache Spark Command Injection Vulnerability
- CVE-2022-28810 (CVSS score: 6.8) – Zoho ManageEngine ADSelfService Plus Remote Code Execution Vulnerability
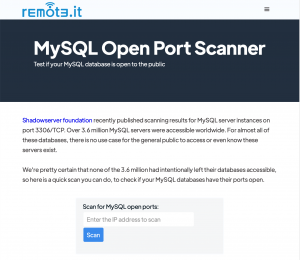
The most critical of the three is CVE-2022-35914, which concerns a remote code execution vulnerability in the third-party library htmlawed present in Teclib GLPI, an open source asset and IT management software package. The exact specifics surrounding the nature of attacks are unknown, but the Shadowserver Foundation in October 2022 noted that it has seen exploitation attempts against its honeypots. Since then, a cURL-based one-line proof of concept (PoC) has been made available on GitHub and a “mass” scanner has been advertised for sale, VulnCheck security researcher Jacob Baines said in December 2022.